Google didn’t prove cryptography is broken; they proved we can now see where it will break.
Recent research from Google Quantum AI is reshaping how we think about quantum computing and encryption. The conversation no longer centers on when quantum computers will break cryptography; it now focuses on something more immediate: identifying cryptographic vulnerabilities that already exist today. This shift introduces a new problem category: Cryptographic Exposure Management (CEM).
CEM is the practice of identifying, prioritizing, and reducing cryptographic risk before it can be exploited.

What Google News Changed
Most discussions around quantum computing still focus on theory—qubits, timelines, and “Q-Day.” That framing is increasingly outdated.
The key change is visibility: we can now measure where cryptographic systems will fail before they actually do, moving quantum risk out of academic debate and into operational reality.
What Did Google Actually Say About Quantum Computing and Encryption?
Across recent work from Google Research, the Google Quantum AI whitepaper, and new research on reducing the quantum resources required to run Shor’s algorithm, a clear pattern is emerging.
The implications become clearer when broken down into three areas:
1. Google Blog Research Findings on Quantum Cryptography Risk
Google does not say that cryptography is broken today. (Read Here)
What they are saying is:
- They can now identify specific real-world conditions where cryptography becomes vulnerable in a quantum future.
- They can prove those risks exist without exposing how to exploit them (using zero-knowledge approaches).
- They believe this is serious enough to justify responsible disclosure now, not later.
Outcome:
Quantum risk is no longer hypothetical. It is something that can be measured, shared, and acted on early.
2. How Google’s Quantum Research Paper Impacts Encryption (ECC and RSA)
This is where the headlines came from. (Read Here)
In simple terms, Google showed:
- Breaking elliptic curve cryptography (ECC), one of the most widely used encryption methods alongside RSA, may require far fewer quantum resources than previously thought.
- Under certain assumptions, attacks could occur in minutes rather than days or years.
- The mechanics of these attacks, including timing windows (such as during transactions), are now better understood.
Outcome:
The “cost” of breaking modern cryptography is dropping faster than expected, and attack paths are now understood, not theoretical.
3. Emerging research (Shor’s algorithm with fewer qubits)
Separate research shows that:
- Future quantum systems may not need millions of qubits.
- Cryptographic problems could potentially be broken with tens of thousands.
Outcome:
Timelines remain uncertain, but the barrier to entry is falling faster than expected, making reliance on outdated assumptions about how far away the threat is increasingly risky.
The Real Extent of Quantum Cryptographic Risk Across Systems
Faster attacks are not the primary shift; the more important development is visibility into where cryptography exists across systems.
For the first time, we can:
- Identify where cryptographic exposure exists
- Understand how that exposure could be exploited
- Estimate which systems fail first
All before a practical quantum computer exists. That’s the shift.
A Better Way to Think About This
This is not just a quantum computing problem; it is a Cryptographic Exposure Management (CEM) problem.
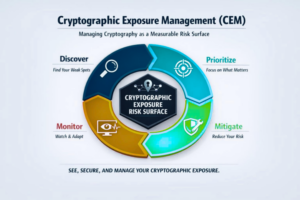
Cryptographic Exposure Management (CEM) is a security discipline focused on continuously identifying and reducing cryptographic risk across systems. This is similar to how organizations manage vulnerabilities or attack surfaces.
CEM is to cryptography what vulnerability management is to software.
Cryptography can no longer be treated as a static control; it must be understood as a dynamic, evolving risk surface. This risk surface must be continuously understood, prioritized, reduced, and monitored.
The risk isn’t created in the future, it is created by how exposed you are today.
What Systems Are Vulnerable to Quantum Computing Attacks?
This is where we have seen most discussions fall short, they stay focused on Bitcoin. The scope is much broader, encompassing any system that relies on public key cryptography.
That includes:
Identity systems, where digital signatures prove who or what something is. If attackers can reverse or forge those signatures, identity stops being trustworthy.
Certificates and PKI, which sit underneath nearly every secure connection. They don’t fail loudly. They continue working, but without real assurance.
Software supply chains, where signed code is assumed to be safe. If signatures can be reproduced, malicious software can look legitimate.
APIs and service-to-service communication, where trust is established cryptographically behind the scenes.
And critically, long-lived encrypted data, intellectual property, healthcare data, financial records, where the risk isn’t immediate access, but eventual exposure after collection.
What Breaks First: How Quantum Computing Impacts Trust Systems
Quantum doesn’t break encryption first. It breaks trust systems and does so quietly.
Identity becomes impersonation.
Certificates become assumptions.
Signed software becomes indistinguishable from malicious code.
Encrypted data becomes a delayed breach.
This is not a sudden failure event, but a gradual degradation of trust over time.
Why this matters now (not later):
None of this means systems are breakable today. It does mean:
- We can identify exposure conditions now
- We understand how attacks will work
- We know which systems are most at risk
This is enough to justify action, because once risk becomes measurable, it becomes manageable.
How to Prepare for Quantum Computing Threats Today
The answer isn’t to panic or wait for perfect standards. It’s to start managing exposure.
Begin with your data. Focus on what needs to remain confidential for years. That’s where quantum risk becomes real.
Next, look at where trust is enforced. Identity, certificates, code signing, system-to-system communication. These are your critical dependencies.
Reduce unnecessary exposure wherever possible. Avoid key reuse. Enforce forward secrecy. Shorten how long keys and certificates live.
Most importantly, build visibility into your cryptographic posture. Even partial visibility is better than none.
Without it, you are guessing, not managing exposure.
What this is not:
This is not an immediate “everything breaks” moment.
This problem is not solved by only adopting new algorithms.
Additionally, it’s not limited to cryptocurrency.
What this actually is:
A shift from cryptography as a static control to cryptography as a continuously managed risk surface.
Final Thought
Google didn’t prove cryptography is broken. They proved we can now see where it will break.
Most organizations are still asking: “When should we migrate to PQC?”
The better question is: “What is our cryptographic exposure today, and how are we managing it?”
FAQ: Quantum Computing and Encryption
Will quantum computers break encryption?
Quantum computers are expected to break widely used encryption methods like RSA and ECC using Shor’s algorithm. However, large-scale practical attacks are not possible yet.
When will quantum computers break cryptography?
Timelines remain uncertain, but recent research from Google suggests the required resources may be lower than previously estimated.
What is post-quantum cryptography (PQC)?
Post-quantum cryptography refers to new encryption algorithms designed to resist quantum attacks.
What is cryptographic exposure management?
Cryptographic Exposure Management (CEM) is the practice of identifying, prioritizing, and reducing cryptographic risk across systems before vulnerabilities are exploited.