Post-Quantum Cryptography Made Simple
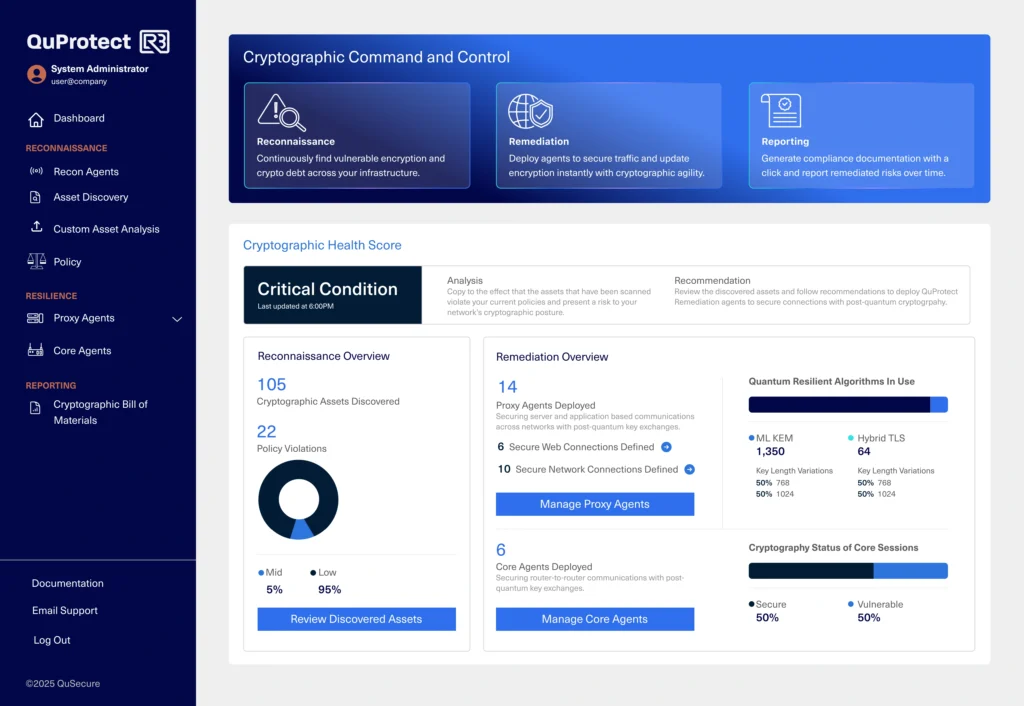
See your vulnerabilities. Secure your systems. Showcase your compliance.
RSA, ECC, and other widely used algorithms are on borrowed time.
The Problem
Most organizations don’t know what cryptography they’re using, where it’s deployed, or whether it can survive what’s coming.


QuProtect

-
The Solution
It delivers real-time discovery, fast remediation, and continuous cryptographic visibility – in a single unified platform.
Deploy QuProtect R3 across cloud, hybrid, on-prem, and air-gapped environments without re-architecting.
See
in Action
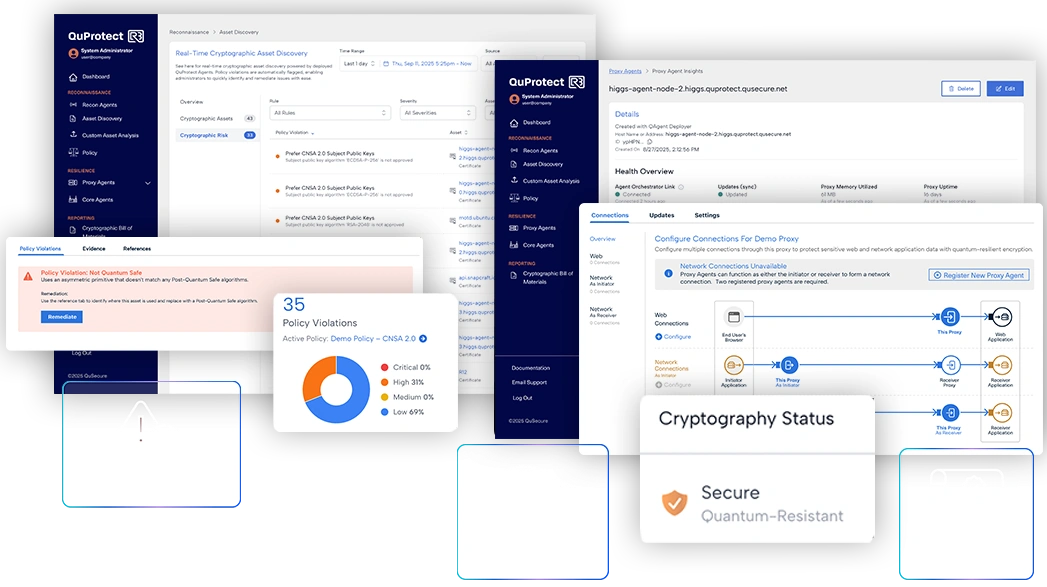
One Platform. Three Core Capabilities.
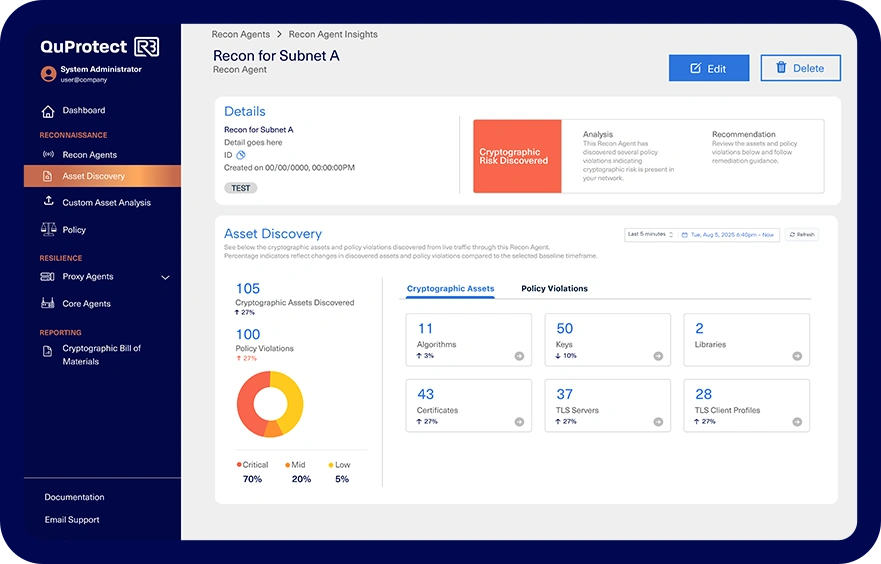
QuProtect Recon –
Discovery Engine
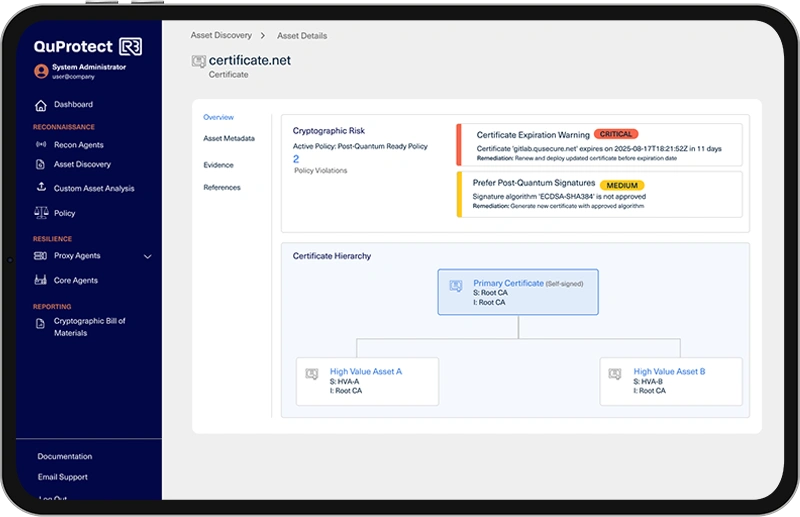
- Instantly scans your infrastructure - network, cloud, applications, endpoints
- Creates a live inventory of in use cryptographic assets and algorithms
- Flags vulnerable, deprecated, or out-of-policy cryptography
- Updates in real time to track posture as environments evolve
- Upload existing inventory for jump start to remediation
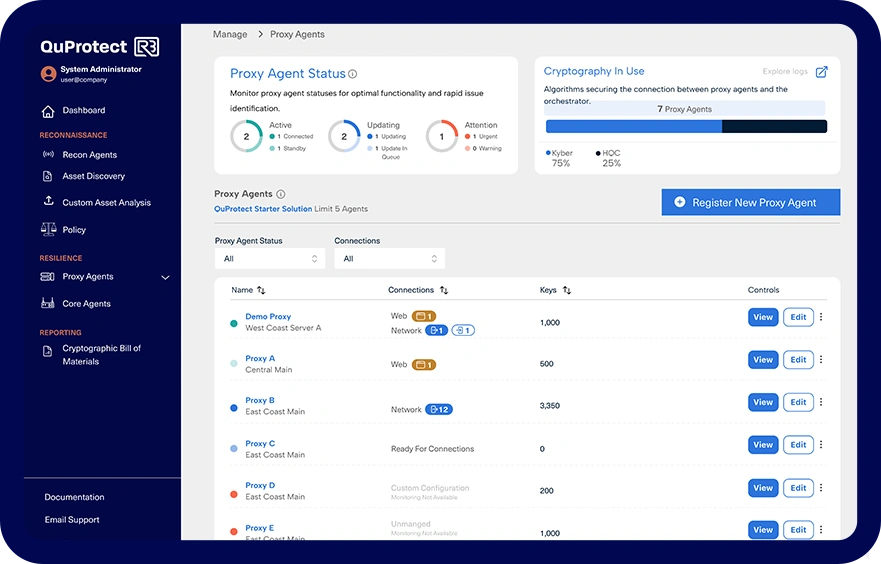
QuProtect Resilience –
Crypto-Agility Orchestrator
- Seamlessly upgrades encryption protocols across devices and systems
- Enables scheduled or on-demand transitions to post-quantum algorithms
- Rapid remediation - no downtime, no code rewrites, no rip-and-replace
- Built to support the latest NIST-approved PQC algorithms
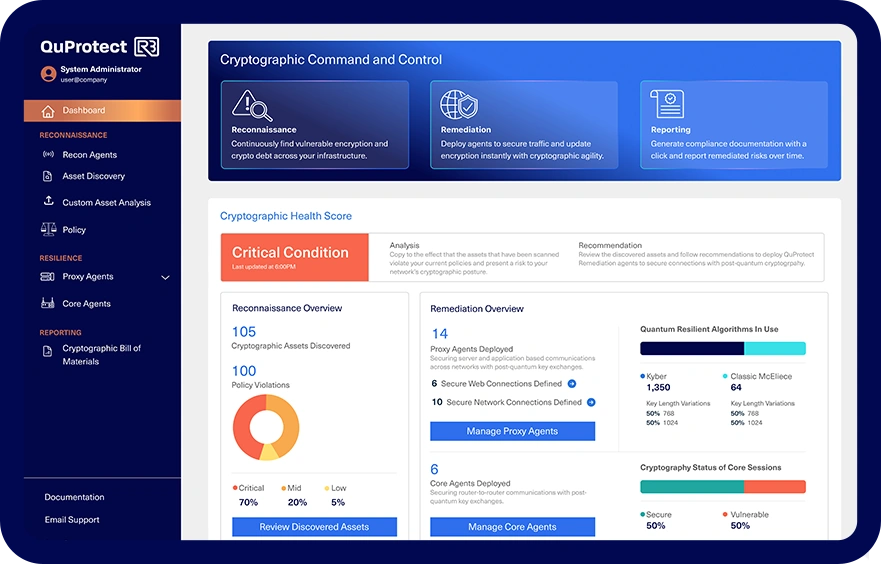
QuProtect Reporting –
Real-Time Compliance Engine
- Generate CBOM (Cryptographic Bill of Materials) with a single click
- Visualizes cryptographic posture trends and risks
- Tracks alignment to NIST, NSM-10, EO 14028, and OMB M-23-02
- Produces audit-ready reports for CISO, CIO, and compliance teams
Crypto visibility and agility controls.
QuProtect

Built For Security and Compliance Leaders
QuProtect R3 is trusted by those who cannot afford to fall behind.
Whether you’re a CISO protecting critical infrastructure, a program manager preparing a federal agency for post-quantum migration, or an enterprise architect modernizing your crypto stack – R3 gives you full control and clear visibility. Designed for sovereign security requirements: deploy in controlled environments and enforce crypto policy without re-architecting.

See
in Action
Schedule a live demo to see the only platform that can help you:
- Discover what’s deployed
- Remediate risk in real time
- Report compliance with confidence
Why
Stands Out
Legacy Scan Tools
Manual Methods
Legacy Scan Tools
- Full Asset Visibility
- Partial
- Live, End-to-End
- PQC Algorithm Detection
- Built-In
- CBOM Generation
- Real-Time
- Continuous Monitoring
- Manual
- Always-On
- Compliance Framework Support
- Partial
- Limited
- NIST, NSM-10 Ready
- Remediation / Crypto-Agility
- Native
- Deployment Time
- Months
- Weeks
- Days
See
in Action
Ready to Take Command?
You’ve seen what’s coming. Now take control before quantum breaks everything.
With
, you can:

Discover what’s
deployed

Remediate risk in
real time